GPO for Bitlocker Drive Encryption and Applying it Automatically
After many frustrating searches and much trawling on the internet I finally found a way to not only set bitlocker drive encryption policies on a domain level. So i am going to detail the selections I have applied below so its all in one place but feel free to add your own settings to your application.
Computer Configuration > Administrative Templates > Windows Components > Bitlocker Drive Encryption
Change the “Store Bitlocker recovery information in Active Directory Domain Services” to enabled and then change the below setting.
Select Bitlocker recovery information to store: Recovery passwords and key packages
Computer Configuration > Administrative Templates > Windows Components > Bitlocker Drive Encryption > Fixed Data Drives
Change the below settings
Configure use of hardware based encryption for fixed data drives: disabled
I selected this due to the issue of hardware encryption being easily bypassed reported a couple of years ago (Bleeping Computer article) and have yet to hear this has actually been resolved so I aired on the side of caution.
Now change “Choose how Bitlocker-protected fixed drives can be recovered” and select the below settings.
Allow data recovery agent: Yes
Configure user storage of Bitlocker recovery information : Allow 48-digit recovery password and allow 256-bit recovery key
Omit recovery options from the Bitlocker setup wizard: Yes
Save Bitlocker recovery information to AD DS for fixed data drives: Yes
Do not enable Bitlocker until recovery information is stored to AD DS for fixed data drives: Yes
Computer Configuration > Administrative Templates > Windows Components > Bitlocker Drive Encryption > Operating System Drives
Apply the same settings you applied to Fixed data drives
Computer Configuration > Administrative Templates > Windows Components > Bitlocker Drive Encryption > Removable Data Drives
And again apply the same settings
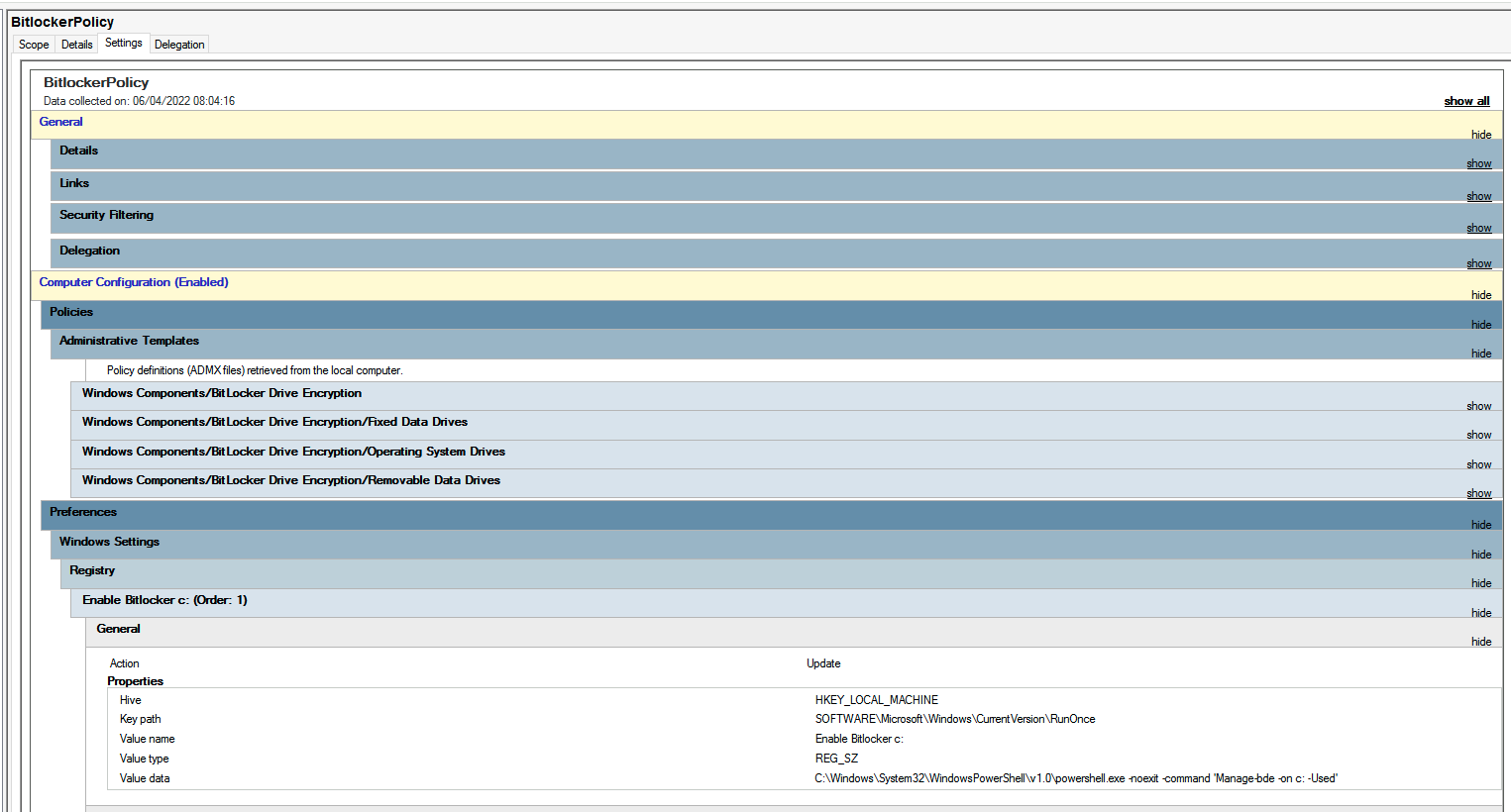
Lastly we now apply a registry key to run a command to encrypt the drive
Computer Configuration > Preferences > Windows Settings > Registry
Now right click and select new registry item. And change the below settings
Action: Update
Hive: HKEY_LOCAL_MACHINE
Key Path: SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
Value name: Enable Bitlocker C:
Value data: C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe -noexit -command 'Manage-bde -on c: -Used'
Hit ok and then repeat on any other drives you would like to encrypt. And now you're done once you configure the security of your gpo bitlocker should now automatically apply and sync the recovery password up to AD.